Solutions
Data Recovery
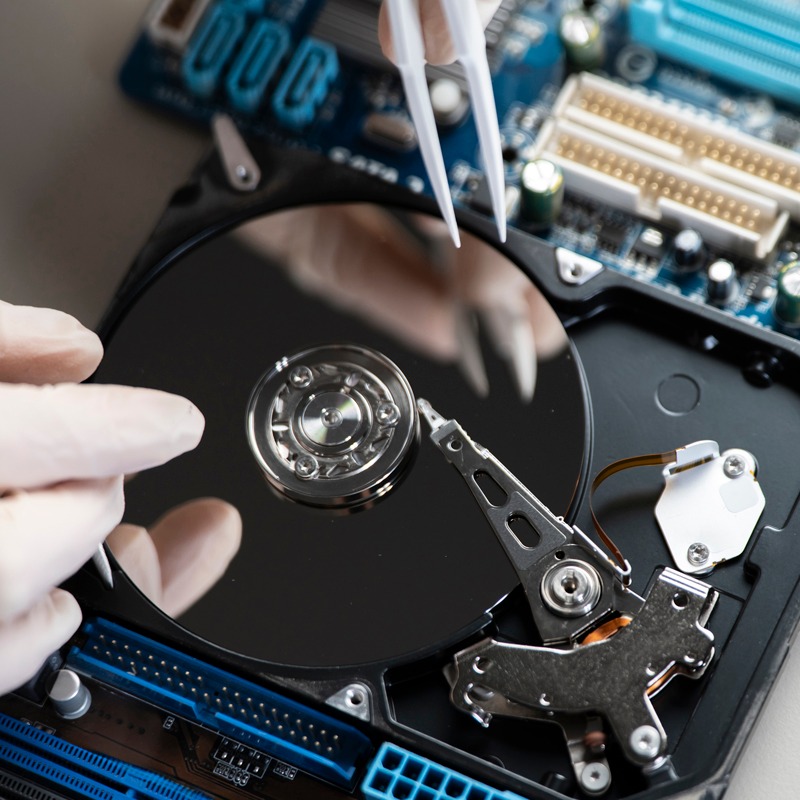
Our Data Recovery solutions are designed to retrieve critical information from failed, damaged, or corrupted storage devices. We handle hard drives, SSDs, servers, RAID systems, laptops, and external storage affected by accidental deletion, formatting errors, hardware failure, or system crashes. Using advanced recovery tools and secure processes, we work to restore valuable business and personal data while maintaining strict confidentiality. Each case is carefully assessed to determine the safest and most effective recovery approach. Our priority is maximizing data retrieval while protecting the integrity and privacy of your information.
Data Sanitization
Our Data Sanitization solutions ensure permanent and irreversible removal of sensitive information from IT assets before reuse, resale, or disposal. We use certified erasure methods that comply with industry standards and regulatory requirements to prevent unauthorized data recovery. Our services cover laptops, desktops, servers, storage drives, and other digital devices. We provide proper documentation and verification reports to support compliance and audit needs. By securely eliminating confidential data, we help organizations reduce the risk of data breaches and maintain trust, security, and regulatory alignment.


Data Cloud
Our Data Cloud solutions provide secure backup, storage, and seamless access to your critical business information. We assist with cloud migration, automated backups, disaster recovery planning, and secure data synchronization across devices and locations. Designed to improve flexibility and business continuity, our solutions help prevent data loss caused by hardware failure, cyber threats, or unexpected disruptions. With strong encryption, controlled access, and reliable infrastructure, we ensure your data remains protected, accessible, and efficiently managed at all times.
Data Security
Our Data Security solutions are built to safeguard sensitive business information from cyber threats, unauthorized access, and internal risks. We implement strong encryption, secure network configurations, firewall protection, endpoint security, and controlled access management. Our approach also supports compliance with regulatory standards such as DPDP and ISO requirements. Through continuous monitoring, risk assessment, and proactive security measures, we help organizations prevent data breaches and maintain operational integrity. Our goal is to create a secure digital environment where your critical data remains protected, confidential, and fully under control.


